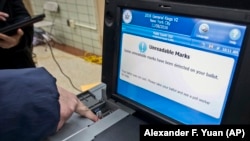
Hackers affiliated with the Russian government conducted an "unprecedented, coordinated" campaign against the U.S. voting system, including successfully penetrating a few voter-registration databases in 2016, a Senate committee has concluded.
The cyberattacks targeted at least 18 states, and possibly three more, the U.S. Senate Intelligence Committee said on May 8 in the first installment of its long-awaited report on alleged Russian meddling in the 2016 election.
Although the committee did not find any evidence that the hackers actually changed votes, it said it found "ample evidence" that the Russian government sought to undermine confidence in U.S. voting systems,.
Moreover, the committee report warns of continuing vulnerabilities and said more attacks were possible. It suggested that the activity uncovered in 2016 might have been simply testing for a future attack.
The committee found that Russia undertook a wide variety of intelligence-related activities targeting the U.S. voting process, beginning at least as early as 2014 and continuing through Election Day 2016.
"In a small number of states, these cyber-actors were in a position to, at a minimum, alter or delete voter-registration data; however, they did not appear to be in a position to manipulate individual votes or aggregate vote totals," the report said.
Illinois is the only state that has publicly disclosed that its voting system was breached. The report does not say which other states' voting systems were successfully hacked.
The Department of Homeland Security and Federal Bureau of Investigation during the election campaign in 2016 alerted states to the threat of Russian intrusion, but the warnings "were limited," the report said.
As a result, it said, while state officials understood there was a threat, they did not understand its scope or seriousness. It said the federal government was now communicating the seriousness of the threat more clearly to state election officials.
The department is now offering, among other things, to do comprehensive risk assessments and remote scanning of state networks to help states spot vulnerabilities.
The release marked the committee's first public report after more than a year looking into whether Russia sought to interfere in the 2016 presidential campaign. Russia denies any interference.
The report released on May 8 was unclassified, but the committee also prepared a classified report on threats to the election infrastructure.
The report recommended that the 50 U.S. states continue to run elections, but it said the U.S. government should bolster state security efforts by "clearly communicating" that it views attacks on U.S. election infrastructure as a hostile act, and will respond accordingly.
The report also said the United States should build a stronger defense against cyberattacks, including more quickly determining who is behind them.